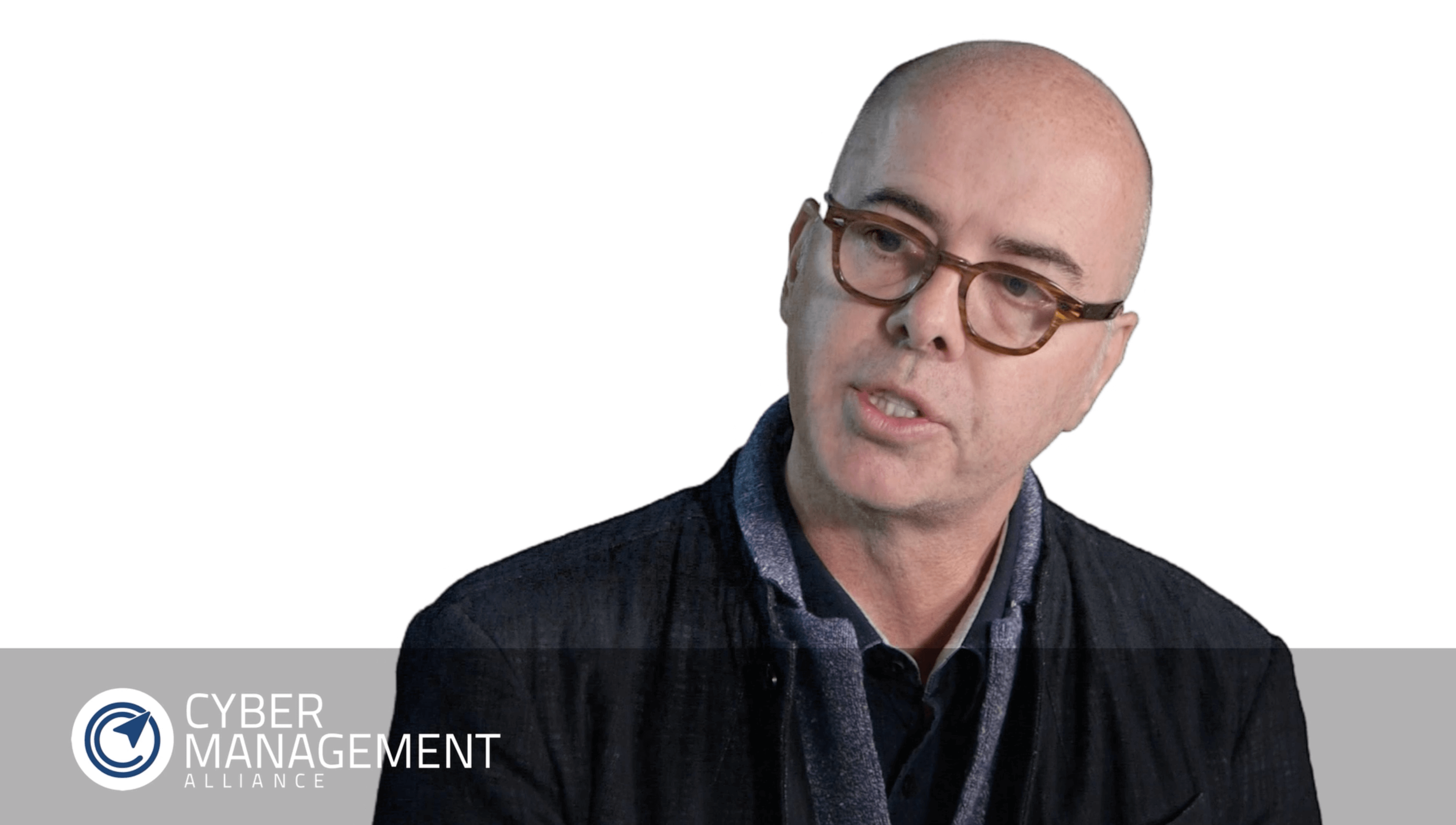
Interview with Tracy Andrew Former Infosec Manager at Fieldfisher LLP
Date: 1 August 2017
As part of Cyber Management Alliance’s exclusive Insights With Cyber Leaders interview series, Amar Singh, CEO of Cyber Management Alliance, sat down with Tracy Andrew, former Information Security and Compliance Manager at one of the largest law firms in Europe - Fieldfisher Waterhouse, to gather fascinating insights into his career, his thoughts on qualifications and certifications, what attributes he looks for when recruiting, and whether, in his opinion, it is important to have a technical background to succeed in cyber security.
Tracy Andrew is not just an Information Security and Compliance Manager at Fieldfisher; as far as he’s concerned, he’s also the Information Security & Compliance Officer, the Data Protection Officer, and a few other things thrown in! Like many CISOs worldwide, Tracy wears many hats so, if it has an information security, data protection or physical security risk, it falls within his remit.
My journey to CISO
Tracy Andrew’s career journey to CISO has, by his own admission, been pretty diverse. At the age of 17, he joined the Army and went into the Military Police where he gained the skills of telecommunications set up and that of a signals instructor.
Later, whilst still in the Army, Tracy joined REME, becoming a telecommunications technician. This role subsequently became digital electronics, and he went on to be the Army’s adviser on computer controlled test equipment. As part of his Army training, and being a signals instructor, he was also an electronic warfare instructor – so, cyber is electronic warfare but on a new platform.
On leaving the army, Tracy worked as a business manager, building and supporting computer controlled test equipment for the Army. Following 12 years with the NHS including the role of Head of Information Governance for Berkshire, Tracy moved into the legal sector with Fieldfisher Waterhouse.
Tracy strongly believes that his combination of business knowledge, information security knowledge, and his years in the public and private sectors, he has developed well-rounded skills that have been the basis of his career.
Do you need a qualification to get into cyber security?
For Tracy, he’s achieved qualifications and certifications including ISO 27001 Lead Auditor, a NEBOSH diploma and Data Protection CIPPE with the IAPP. He is also a full member of the IISP (Institute of Information Security Professionals) and is data protection qualified with PC in Freedom of Information (Practitioner Certificate in Freedom of Information). And for Tracy, he would always use ISO 27001 as his baseline. He says:
“It’s not necessarily an absolute must but if I didn’t certify, I’d use it as a compliance tool, as my benchmark to ensure that all of the main features are covered including nothing moves without risk assessment, have I got the right access controls and how do I control my third party access?”
Third party access – a good move by the Government to make it mandatory?
In Tracy’s opinion, the Government highlighting third party access and making their Cyber Essentials Scheme mandatory for all government contracts this year is a good move. It raises the profile of third party risk and cyber security within an organisation, and with users. Tracy quotes Charlie Martin and adds:
“There is no patch for human stupidity. So, in other words, whatever policies and procedures are in place, whatever you do technically, at the end of the day there is a human finger that clicks on accept, or on a website, or a link.”
So far, there’s been a very low uptake of the Cyber Essentials Scheme but with it becoming mandatory, there’s going to be a sudden stampede for accreditation. As far as Tracy is concerned, it’s simple, it’s basic, and people should be able to do it. It is a good place to start for small and medium sized businesses and could potentially reduce an organisation’s risk by up to 80%.
Personal certifications – is there a particular certification for a IT user/non-IT user that they need to focus on?
For Tracy something like CISSP is not the most applicable as he admits he’s not in-depth technical but he does think it’s appropriate for technical people to have that qualification.
For non-technical people, Tracy believes that CISM is probably more but there’s also the IAPP (International Association of Privacy Professionals) who provide the Certified Information Privacy Practitioner for Europe certification, which is the data protection, and CIPM – Certified Information of Privacy Manager. Tracy personally advocates the ISO 27001 Lead Auditor and Lead Implementer certifications as they make you ask questions.
What do you look for in your ideal candidate?
Tracy looks for people with passion, drive, determination and innovation, those that are outside the box thinkers. He doesn’t want the corporate mindset and follow instinct, but those that will challenge and ask questions.
Qualifications are a tick box but they are not the be all and end all. Experience is key; what have they done? What have they achieved? Just because they’re not qualified doesn’t mean that Tracy wouldn’t consider them for the role if they are prepared to go that extra mile and challenge the corporate line.
“If we do everything the same way every time, we not going to solve all the problems. So, if someone comes up with a novel, innovative way of doing things, to me, they may be a better candidate.”
Is it really necessary to be technical to enter cyber security?
Tracy believes that as long as you have a fundamental grasp of what IT is, that you can speak the languages of business and engaging with users, and are able to hold a technical conversation with the IT guys at a reasonable level, then no, you don’t need to be technical to succeed in cyber security, although a technical overview helps. That said, he adds that those that are too technical can sometimes get buried in the detail and may not see the bigger picture as effectively as one that is not so technical.
To view Tracy Andrew’s Insight With Cyber Leaders exclusive interview in full, click here.
For more information on Cyber Management Alliance, their CIPR training, Live Online CISSP Training & Mentorship program and other GCHQ-accredited courses, webinars, the Wisdom of Crowds live and virtual events, and their Insights with Cyber Leaders series of exclusive interviews, click here or contact us today.