ERP Cyber security - Will CISSP qualification help?
Date: 6 May 2016

In the current business scenario, virtually every ERP application is vulnerable to unauthorised access, financial fraud, sabotage or espionage (leakage of industry secrets) from cyber-attacks targeting these business-critical enterprise systems.
Recently, on 11 May 2016, the United States Department of Homeland Security's internal Computer Emergency Readiness Team (CERT) sent an alert warning that at least 36 unnamed organisations are running misconfigured or outdated SAP software, which could leave them prone to remote attacks by hackers.
An affected enterprise is said to be one of the Top Ten highest annually-grossing global companies, and more than a dozen generate over $10 billion in annual revenue per year. According to the alert, a hacker that successfully exploits the vulnerability can gain full access and complete control to an affected SAP platform - that includes business information and processes on those systems.
These ERP boxes are a bloodline of large organisations as they manage their most sensitive information and processes, such as Procure to Pay (you buy raw material from supplier), Order to Cash (selling finished goods) and general accounting/financial accounting. These ERP systems also host HR information and thus, employee records.
Question is, what qualification should a person possess to safeguard these critical ERP systems?
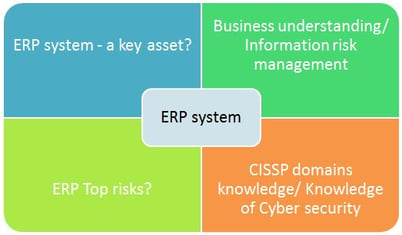
Before I jump to the conclusion, it is important one understands the following:
- What is an ERP system and why this system is so critical?
- What are the key challenges CISO's and organisations are facing in safeguarding ERP systems?
- What are the top risks in current ERP systems?
- What controls/skills are required to address these issues and how CISSP will help?
Figure 1: ERP Cyber Security - what you need to understand
In answer to the above questions, there really is no one thing that will help you implement all of your security requirements. You need a techno-functional person who can understand business processes, sensitivity of business information and the backend technology (networks, databases, switches, server architecture, data flows, connections, etc.) to design a defense in-depth architecture to protect your ERP environment.
Figure 2: Blend of Techno - functional skills to implement ERP Cyber Security
In this blog, I have created a mind map that answers the above questions in detail and will also help you to understand how CISSP qualification (knowledge on various domains) will help you prepare for a job in this sector.
From ISC2
CISSP certification belongs to ISC2. ISC2 has a vision to "Inspire a safe and secure cyber world."
To explore more on CISSP domains - Click here to access the CISSP official page on ISC2.
From ISACA
ISACA has released a guidance document with an objective to enable audit, assurance, risk and security professionals (Information Technology [IT] and non-IT) to evaluate risk and controls in existing ERP implementations, and to facilitate the design and building of better practice controls into system upgrades and enhancements.
Author:
The author is a professional CISSP trainer trainer within CMA training pool. He is CMA's CISSP/CISA/ISO 27001/SOX/Information Risk Management/SAP Cyber Security trainer. He has an MBA (Finance), Computer Engineering, CISSP, CISA, ITIL (expert), COBIT (foundations), and SAP security qualifications.
If you are interested in exploring our CISSP mentorship online and classroom program details – please follow below link.
You can also follow us on twitter - https://twitter.com/cm_alliance
And connect with us on linkedin - https://www.linkedin.com/company/10003478/
Please let us know if you are facing difficulty in accessing mind map.